Content
Introductory
Even in the best family, the person may type their password or the password copied to the clipboard may not have been correct, causing the system to disable IP addresses. Well, I did the same the other day while I was setting up my email addresses. Of course it's one FTP it can also happen with login, HTTP authentication, or with any internet service where you have to enter your password.
In this little description, it happened to me IMAP disabling an IP address that occurred when setting up a mailbox, I describe resolving the fact that if someone else is in a similar situation and suddenly there is no solution at hand, this writing can save you a few more searches on the Internet.
Of course, this only works if we run the server ourselves, from which our IP address has been banned from one of the services, so we have (root) SSH access, and Fail2Ban program is also running on the server. In my case, specifically, it worked well In an ISPConfig server environment blocking occurred, which I was even happy to know later, knowing that the programs running on the server were doing their job well.
Making a mistake
One late night I set up my email addresses in a freshly installed Mozilla Thunderbird email client, set up three already, and then did a bit more checking than the following:
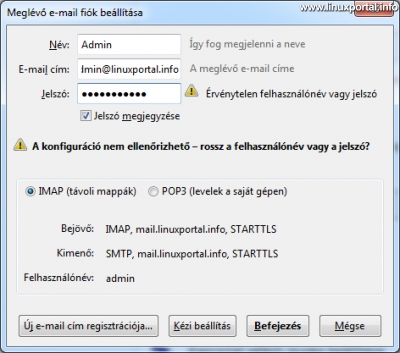
Then the password is checked and then the error is thrown:
Then I copied my generated password again from my password store and started over again. I thought it would happen to anyone, no problem with that.
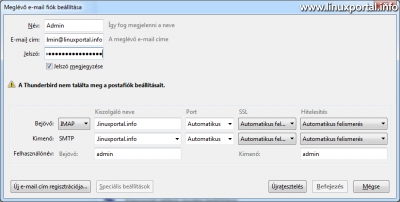
But then, when he was not good the third time, he put in a window like this:
Well, from now on I could do anything, it wasn't good. In the meantime, I dropped my email address and tried another one's password. But you have already entered it with a good password.
What was interesting was that the email addresses that I had set up were synchronized nicely, so I didn't even think about blocking my IP address or anything like that at first.
Troubleshooting
Since I'm no longer at this point, I say I'll look around the server. I logged in as root and first looked at the end of /var/log/mail.log:
cat /var/log/mail.log | tail -40And I found my IP address in the error message lines:
... postfix/submission/smtpd[16279]: improper command pipelining after EHLO from <ip-címem>: QUIT ... dovecot: imap-login: Disconnected (auth failed, 3 attempts in 26 secs): user=<email címem>, method=PLAIN, rip=<ip-címem>, lip=<szerver IP-címe>, TLS, session=... ... postfix/anvil[12691]: statistics: max connection rate 4/60s for (submission:<ip-címem>) at ... ... postfix/anvil[12691]: statistics: max connection count 2 for (submission:<ip-címem>) at ...
Well, then I say head to the firewall:
iptables -LAz iptables issued the chains at the lister's command, with many other blocked IP addresses in them, of course, like flies on creature paper, and of course I found my own here in the fail2ban-dovecot-pop3imap chain:
Chain fail2ban-dovecot-pop3imap (1 references) target prot opt source destination REJECT all -- <IP-címem> anywhere reject-with icmp-port-unreachable RETURN all -- anywhere anywhere
Only my own title was sitting in this chain, so I just had to unlock it.
Resolving a blocked IP address
An easy solution here would have been to remove the blocked IP address with the appropriate command from iptables, but since Fail2Ban put it on the list, it would not have been advisable to reach in, and in that case you should contact Fail2Ban.
I have already made a description of the About managing filters in Fail2Ban, where I was just setting up another jail, and here first I needed the exact names of the jails to reference the correct one because I didn't remember the names exactly:
fail2ban-client statusStatus |- Number of jail: 7 `- Jail list: postfix-sasl, dovecot-pop3imap, apache-noscript, ssh, pureftpd, apache, apache-multiport
It was also: dovecot-pop3imap the name of my jail (there was only one "prefix in" fail2- "in iptables). I looked at my jail:
fail2ban-client status dovecot-pop3imapStatus for the jail: dovecot-pop3imap |- filter | |- File list: /var/log/mail.log | |- Currently failed: 1 | `- Total failed: 7470 `- action |- Currently banned: 1 | `- IP list: <ip-címem> `- Total banned: 9
My address is booming here, so it was only one step to get it right fail2ban-client command:
fail2ban-client set dovecot-pop3imap unbanip <ip-címem>Then I looked at the status of the jail again with the previous command and it no longer had my address:
Status for the jail: dovecot-pop3imap |- filter | |- File list: /var/log/mail.log | |- Currently failed: 1 | `- Total failed: 7470 `- action |- Currently banned: 0 | `- IP list: `- Total banned: 9
After that I was able to set up my email address correctly with the correct password.
Conclusion
In retrospect, it took a single command to think of it all, but then, in the first few minutes, one had to think about where to go. So practicing was definitely good, so if you re-use it with another service, such as FTP, you'll get the IP address right from the right jail.
However, if SSH is similarly blocked and you are unable to access the console, you will have to wait for your own configuration bantime time because we will not get near our favorite terminal until then. Therefore, in order to prevent SSH from occurring in any way, I highly recommend password-free authentication key entry method.
- Encyclopedia - Fail2Ban
- Fail2Ban (manual page)
- Iptables (manual page)
- How to enable Fail2Ban program filters in the ISPConfig server environment
- Enhance SSH protection with additional Fail2Ban filter patterns on Debian 8 (Jessie)
- How to keep unwanted robots away from our server websites
- How to protect our server from attacks on our databases with "Access denied for user root@ip address (using password: YES / NO)" using Fail2Ban
- What should we do if our Matomo web analytics system generates "AH01630: client denied by server configuration" type Apache errors that causes Fail2Ban to block our IP address?
- How to defend against attacks resulting in large volumes of 404 or other 4xx HTTP error codes with Fail2Ban
- Perfect server: Debian 8 (Jessie) V1.0
- Perfect server: Debian 9 (Stretch) V1.0
- Perfect server: Debian 10 (Buster) V1.0
- To post registration and login required
- 2323 views